Ah, internet scams. They’re everywhere these days and, as you can imagine, they are increasingly sophisticated in their attempts to fool you into handing over hard-earned cash. One of the most recent to emerge presents you with one of your own passwords as well as a lurid story about internet surfing habits in an effort to scare you into paying money to the scammer.
Without going into the gory details of that particular scam (because it is just one example of many), it does serve to highlight the necessity for two-factor authentication (2FA) for all your online accounts and services. With businesses relying on emails as its main communication tool, and hackers being aware of this, it’s an excellent idea to enable 2FA for your Outlook emails, too.
If you’re not familiar with 2FA, here’s an explanation of what it is
(and why your business needs it)
Typically, you’d log on to online services or your email using a username and password. That’s well and good, but time and time again, we see massive data breaches where these details are compromised en masse. Journalist Taylor Armerding at CSO Online has helpfully documented the biggest hacks of the 21st century; topping the list is Yahoo, which had 3 billion accounts compromised. Including usernames and passwords. Ouch.
It’s the countless compromised passwords, by the way, which are now emerging in scams like the one in the first paragraph. By presenting you with one of your own passwords, you’re more likely to be scared into believing the miscreant actually has something on you, when they probably do not.
But back to 2FA. In the past, 2 Factor authentication solutions evolved around hardware – such as a hard token-based services like RSA SecurID. In 2018, adding an extra layer of protection is easier than ever! Major vendors such as Microsoft & Google are adopting the use of virtual tokens. These are basically apps installed on your mobile device, providing the same log-in token as a physical device would.
This goes a step beyond the username and password combo, which if you read Armerding’s article is starting to look notoriously unreliable, and adds an extra layer, or factor.
- The first factor is something you know - that’s the aforementioned username and password.
- The second factor is something you have (a token, barcode, etc) or something you are (a fingerprint, retina scan, etc).
As you’ll appreciate, it becomes much, much harder for a hacker to get hold of your fingerprints, mobile phone or eyeballs to add to their trove of usernames and passwords.
The burning question, then, is how to introduce 2FA?
Here’s some good news for Office 365 users (which makes up the vast majority of business email hosting these days): you can turn 2FA for your Outlook emails easily with the help of an IT provider.
Included within the Office 365 plans for free, the solution can provide big assurance for your users and your company. Just like any change, getting used to the additional steps to access your inbox can be a little daunting at first. That's why, we thought a visual of the step-by-step process could be a great start to encourage you to take the leap.
A step-by-step overview of using 2FA for your 365 business emails
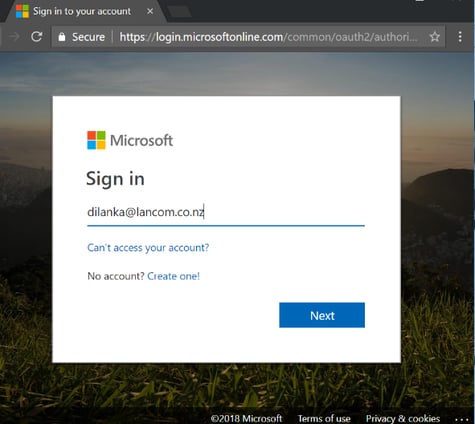
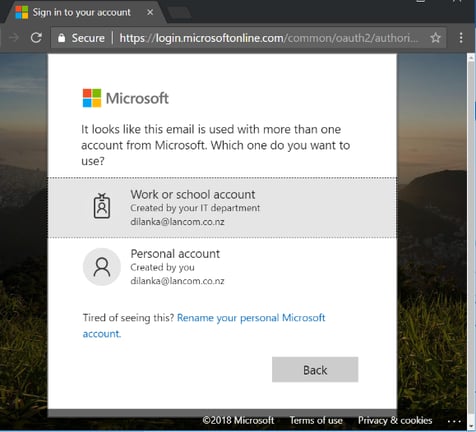
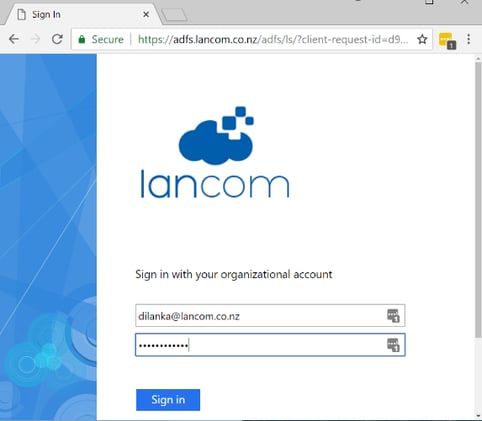
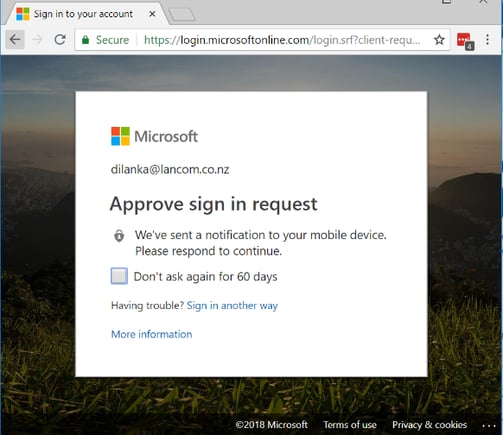
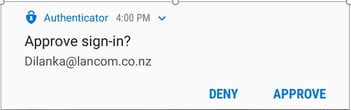
When you access your emails via Outlook or the Microsoft portal at https://portal.microsoft.com, you will start to see a few new screens, which are mainly there to add the extra layer of protection we have been discussing in this post. Using an app, called Microsoft Authenticator (which gets installed on your mobile device just like any other app), the 2FA system will flick you a pop-up notification to approve the sign-in process.
There are also another ways to approve the login, like the classic text with a magic number to unlock your door to emails. The preference is ultimately yours, based on what you would feel most comfortable with.
From there, the process is a simple as going through the screens!
We are big fans of IT security that adds value and ensures safety. Having a cyber-security plan in place can start with simple steps, such as turning on 2FA for your email systems, as seen in this post.
If you are feeling overwhelmed with the options in the market, then a chat with a professional is the starting point.
Draft an IT security plan that suits your business. Book a commitment free review with us here.





